APPLICATIONS
HOT NEWS
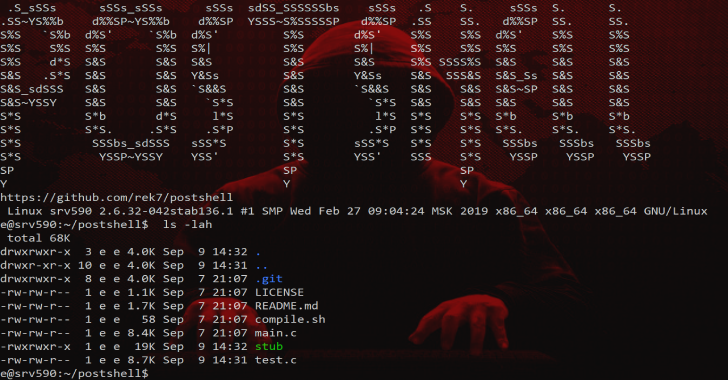
PostShell – Post Exploitation Bind/Backconnect Shell
PostShell is a post-exploitation shell that includes both a bind and a back connect shell. It creates a fully interactive TTY which allows for...
© kalilinuxtutorials.com 2025





.webp)
%20(1).webp)


.webp)
.webp)