In the intricate realm of cyber threats, GootLoader emerges as a formidable challenge. This article delves deep into the intricacies of decoding its payloads and obfuscations.
Equipped with hands-on scripts and tools, we aim to guide cybersecurity enthusiasts and professionals through the maze of GootLoader. Get ready for an informative journey.
GootLoaderAutoJsDecode.py– automatically decodes.jsfiles using static analysis (recommended)GootLoaderAutoJsDecode-Dynamic.py– automatically decodes.jsfiles using dynamic analysisGootLoaderManualJsDecode-Dynamic.py– used to manually decode.jsfiles using dynamic analysisGootloaderRegDecode.py– automatically decodes reg payload exportsGootloaderWindowsRegDecode.ps1– Directly decodes a payload from the registry.
Index
JavaScript Decoding
Automated Decoding
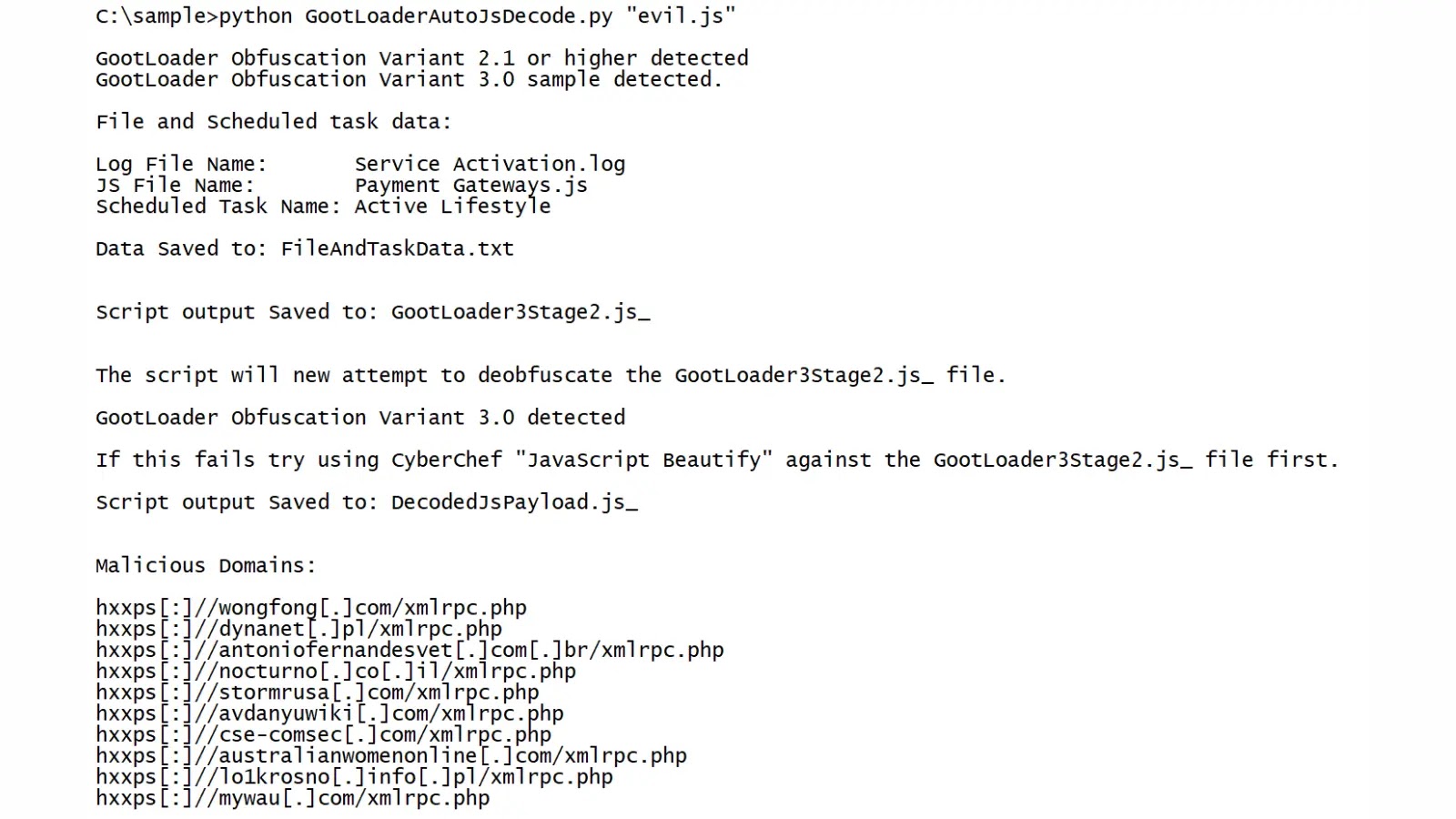
Run the script GootLoaderAutoJsDecode.py against the .js file.
python GootLoaderAutoJsDecode.py "evil.js"The script will output the files below:
FileAndTaskData.txt– Contains the names of the scheduled task and dropped files.DecodedJsPayload.js_– The decoded payload that runs a PowerShell command. You can use a CyberChef’sGeneric Code Beautifyin order to make the content easier to read.
If the GootLoaderAutoJsDecode.py script stops working then you can attempt to use the dynamic version of the script (GootLoaderAutoJsDecode-Dynamic.py). Be aware that the dynamic script executes part of the GOOTLADER code, as a result it should only be run in an isolated environment.
Manual Decoding
Sometimes the GOOTLOADER js obfuscation changes and the GootLoaderAutoJsDecode.py script stops working. In those instances, follow the instructions found at ManualDecoding.md.
Sample MD5s:
Gootloader Obfuscation Variant 2:
82607b68e061abb1d94f33a2e06b0d20
961cd55b17485bfc8b17881d4a643ad8
af9b021a1e339841cfdf65596408862d
d3787939a5681cb6d6ac7c42cd9250b5
Gootloader Obfuscation Variant 3:
ea2271179e75b652cafd8648b698c6f9
c07b581fde56071e05754eef450dfa17Registry Payload Decoding
Redline
- On the left menu go to
Agent Events\Registry Key Events - Filter on the following:
- Change Type:
value change - Path:
HKEY_USERS\<USER_SID>\SOFTWARE\Microsoft\Phone\%USERNAME%- The specific path might change, but you should end up with two sets of keys, one called
...\Phone\UserName\...and one called...\Phone\UserName0\....
- The specific path might change, but you should end up with two sets of keys, one called
- Change Type:
- Select all the rows that have something in the
Text Datafield. - Right click and select “Copy with Headers”
- Paste the text into a text document and save it as a CSV

Decoding The CSV File
- Transfer the CSV and Python scripts to the same machine
- Run the command below:
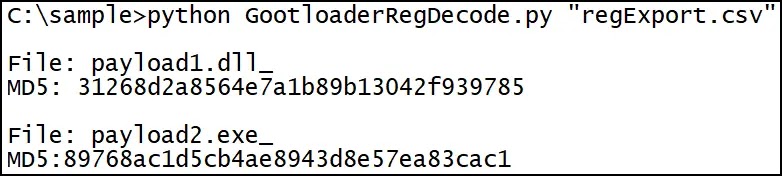
python GootloaderRegDecode.py "regExport.csv"3. The script should generate 2 files payload1.dll_ and payload2.exe_






.jpg)