APPLICATIONS
HOT NEWS
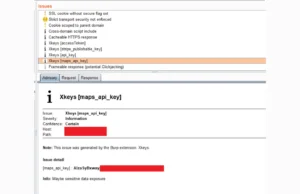
BurpSuite-Xkeys : Mastering Key And Token Extraction For Web Security
Xkeys is a Burp Suite extension designed to extract interesting strings such as keys, secrets, and tokens from web pages. It operates as a...
© kalilinuxtutorials.com 2025







.webp)
.webp)

.webp)
.webp)

.webp)
.webp)