APPLICATIONS
HOT NEWS
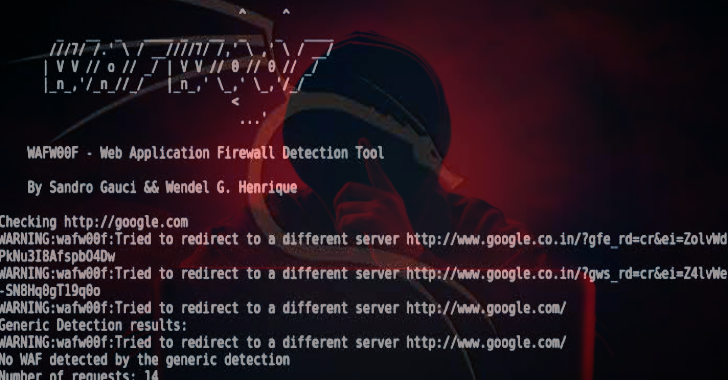
Wafw00f : Identify & Fingerprint Web Application Firewall
WAFW00F allows one to identify and fingerprint Web Application Firewall (WAF) products protecting a website. To do its magic, WAFW00F does the following:
Sends...
© kalilinuxtutorials.com 2025





.webp)

.png)
.png)
.png)