APPLICATIONS
HOT NEWS
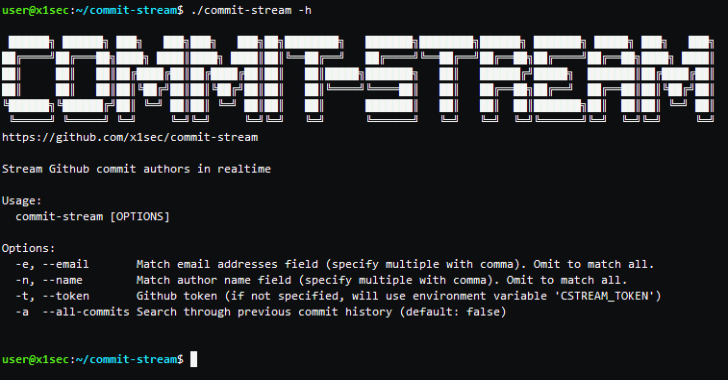
Commit-Stream : OSINT Tool For Finding Github Repositories
Commit-Stream drinks commit logs from the Github event firehose exposing the author details (name and email address) associated with Github repositories in real time.
OSINT...
© kalilinuxtutorials.com 2025