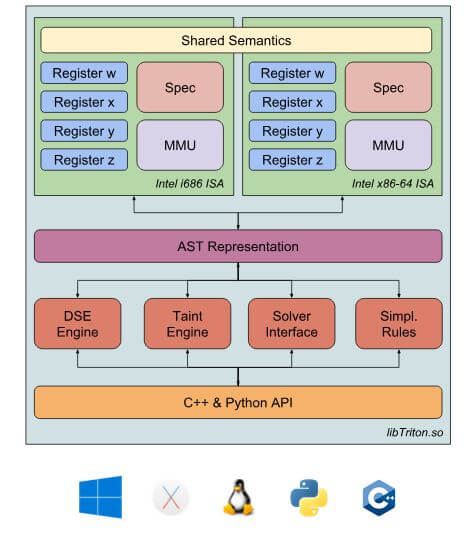
Triton is a Dynamic Binary Analysis (DBA) framework. It provides internal components like a Dynamic Symbolic Execution (DSE) engine, a Taint Engine, AST representations of the x86 and the x86-64 instructions set semantics, SMT simplification passes, an SMT Solver Interface and, the last but not least, Python bindings.
Based on these components, you are able to build program analysis tools, automate reverse engineering and perform software verification. As it is still a young project, please, don’t blame us if it is not yet reliable. Open issues or pull requests are always better than troll =).
Also ReadMiasm – Reverse Engineering Framework In Python
Support
- IRC: #qb_triton@freenode
- Mail: triton at quarkslab com
Cite Triton
@inproceedings{SSTIC2015-Saudel-Salwan,
author = {Florent Saudel and Jonathan Salwan},
title = {Triton: A Dynamic Symbolic Execution Framework},
booktitle = {Symposium sur la s{\'{e}}curit{\'{e}} des technologies de l'information
et des communications, SSTIC, France, Rennes, June 3-5 2015},
publisher = {SSTIC},
pages = {31--54},
year = {2015},
}![]() Credit: Jonathan Salwan, Pierrick Brunet, Florent Saudel & Romain Thomas
Credit: Jonathan Salwan, Pierrick Brunet, Florent Saudel & Romain Thomas
You can follow us on Linkedin, Twitter, Facebook for daily Cybersecurity updates also you can take the Best Cybersecurity courses online to keep your self-updated.










.png)

