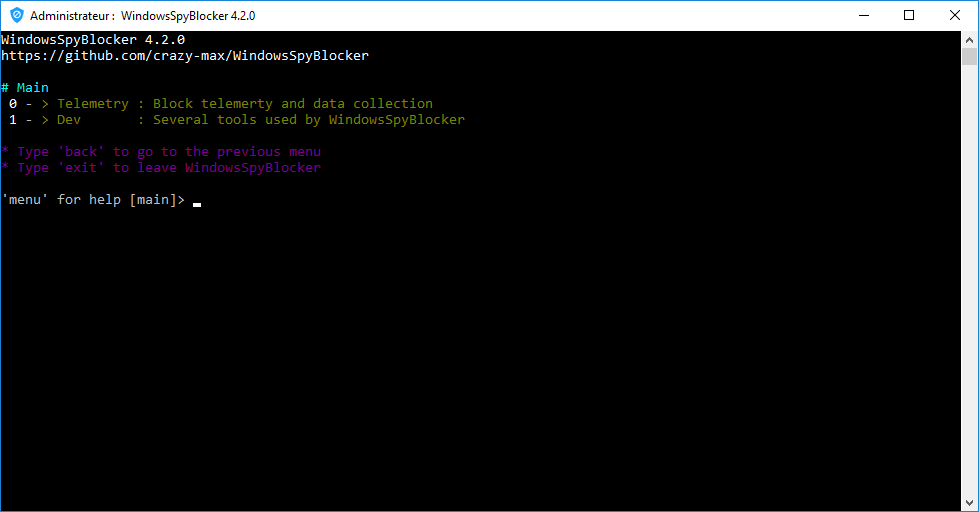
WindowsSpyBlocker is an application written in Go and delivered as a single executable to block spying and tracking on Windows systems. The initial approach of this application is to capture and analyze network traffic based on a set of tools.
Configuration file app.conf is generated at first launch :

Also Read Shodanwave – Tool For Exploring & Obtaining Information From Cameras
WindowsSpyBlocker Telemetry & Data collection
To capture and analyze network traffic for the telemetry option, QEMU virtual machines are used on the server virtualization management platform Proxmox VE based on :
- Windows 10 Pro 64bits with automatic updates enabled.
- Windows 8.1 Pro 64bits with automatic updates enabled.
- Windows 7 SP1 Pro 64bits with automatic updates enabled.
Traffic dumps are clean every day and compared with the current rules to add / remove some hosts or firewall rules.
Tools used to capture traffic :
qemu -net dump: capture- Wireshark : capture + logs
- Sysmon : capture + logs
- Proxifier : logs
The data folder contains the blocking rules based on domains or IPs detected during the capture process :
data/<type>/extra.txt: Block third party applicationsdata/<type>/spy.txt: Block Windows Spy / Telemetrydata/<type>/update.txt: Block Windows Update
Firewall and Hosts data are the main types. The others are generated from these as :
- DNSCrypt : a protocol for securing communications between a client and a DNS resolver.
- OpenWrt : an open source project used on embedded devices to route network traffic.
- P2P : a plaintext IP data format from PeerGuardian.
- Proxifier : an advanced proxy client on Windows with a flexible rule system.
- Simplewall : a simple tool to configure Windows Filtering Platform (WFP).











