When you look at a network PCAP (Packet Capture) file, you look at the network traffic data that was recorded during a certain time period. Tools that record packets, such as Wireshark, tcpdump, and tshark, often make PCAP files. These files have raw network packet data, like headers and payloads, that can help with problems, security, and other things. Here are some ways to look at a PCAP file:
How you can analyze a PCAP file:
Open the PCAP file:
To open the PCAP file, use a tool for packet analysis like Wireshark. Wireshark is easy to use and is used by a lot of people. It lets you see and break apart individual packets, sort data, and look at protocols.
Basic Inspection:
When you open the PCAP file, you’ll see a list of the packets that have been recorded. Each packet’s timestamp, source and destination IP addresses, source and destination ports, protocol, packet length, and other details are shown. This simple information helps you get an idea of the network traffic that has been captured.
Protocol Analysis:
PCAP files can show what different protocols are being used in a network. Wireshark can usually figure out the protocol for each file, which can help you understand how communication works. Look for TCP, UDP, HTTP, DNS, ICMP, and other popular protocols. Look at the details of the procedure to find patterns or oddities.
Filtering:
Use the filtering features of Wireshark to focus on certain packets or kinds of traffic. You can filter by IP address, port, protocol, or other factors, for example. Filtering helps you focus on the most important bits to look at, which makes it easier to spot problems.
Traffic Patterns:
Look at patterns and trends in traffic. Look for sudden drops in traffic or travel patterns that don’t make sense. This can help find network traffic problems, possible DDoS attacks, and other strange things.
Latency and Response Time:
Look at the time between packets to see if contact is taking too long. Latency problems can be signs of slow networks or bottlenecks.
Reassembled Streams:
Some protocols, like HTTP, divide data into different packets. Wireshark can put these packets back together to show you the whole stream of data. This is especially helpful when looking at how people use the web.
Security Analysis:
Look for signs of bad behavior in the PCAP. Look for communication that doesn’t make sense, trends that don’t make sense, IP addresses that seem suspicious, and other signs of a breach or attack.
Troubleshooting:
When looking at the PCAP to fix network problems, pay attention to error messages, failed connections, retransmissions, and other signs that something is wrong.
Expert Information and Statistics:
Wireshark gives you expert information and statistics that can point out problems or strange things in the network flow. This can include warnings about packets that aren’t in the right order, repeated ACKs, and other things.
Follow TCP Streams:
With Wireshark, you can watch the whole TCP stream of a link. This can help you figure out what is going on in a conversation.
Exporting and Reporting:
After you’ve looked at the PCAP file, you might want to export some packets or a rundown of the information so you can look into them further or report on them.
Keep in mind that analyzing PCAP files can be hard and often takes a deep understanding of how networks work and how their protocols work. It’s important to understand the results in the context of how your network is built and how it works.
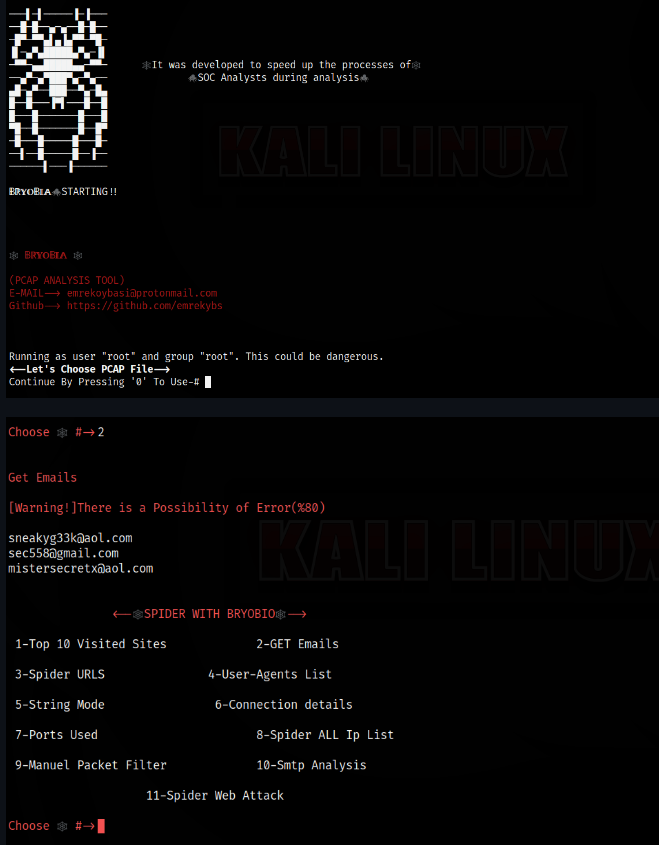
Bryobio
Requirements
$ pip install pyshark
$ pip install dpkt
$ Wireshark
$ Tshark
$ Mergecap
$ Ngrep
???????????????????????????????????????????????? ????????????????????????????????????????????????
$ https://github.com/emrekybs/Bryobio.git
$ cd Bryobio
$ chmod +x bryobio.py
$ python3 bryobio.py

.webp)







.webp)


.webp)








