Using Burp Intruder to Bruteforce passwords.
Burpsuite is a collection of tools and plugins for any web application security testing bundled into a single executable jar file. It contains about 8 useful tools for performing spidering, fuzzing, decoding etc. But the prime feature is that, it is an intercepting proxy which works on application layer. So even HTTPS connections passing through burpsuite are visible. In this article, we will see how to use burp intruder to bruteforce inputs in a web application. For those who are new to burpsuite, read this article on Getting started with Burpsuite. Others can proceed straightaway.
Burp Intruder
The burp intruder is a feature in burpsuite which helps to perform extensive fuzz testing. It helps us to enumerate varaious parameters in a request with supplied wordlist. From password bruteforcing to XSS testing, we can perform all kinds of fuzzing using this amazing plugin in burpsuite.
How Intruder works ?
In order to get started with intruder, we need to get the request captured. This can be a GET or POST request depending on the web-application. Once the rwquest is captured, it can be sent to intruder. Then intruder analyses variable positions in the request where a payload can be inserted. The payload is simply a wordlist we supply. After the wordlist is supplied, the intruder can run through all the combinations in the wordlist on the positions set.
Lab Setup
For this tutorial I am using Mutillidae as the target, Burpsuite running on Kali as attacker. Mutillidae download link is given at the end of the tutorial.
Target : OWASP-BWA – Mutillidae – IP=10.0.2.4
Target URL: 10.0.2.4/mutillidae/index.php/page=login.php
Attacker: Kali Linux 2.0 – IP=10.0.2.5
Lab 1: Brute force Login Form
In this, lab a simple brute-force against a password is performed. This tutorial shows performing this on mutillidae. You can perform this on any login form.
Step 1: Setup Burp as Intercepting Proxy
For this you need to setup the burp as proxy first. If you are not clear on this, refere to Getting Started with Burpsuite article.
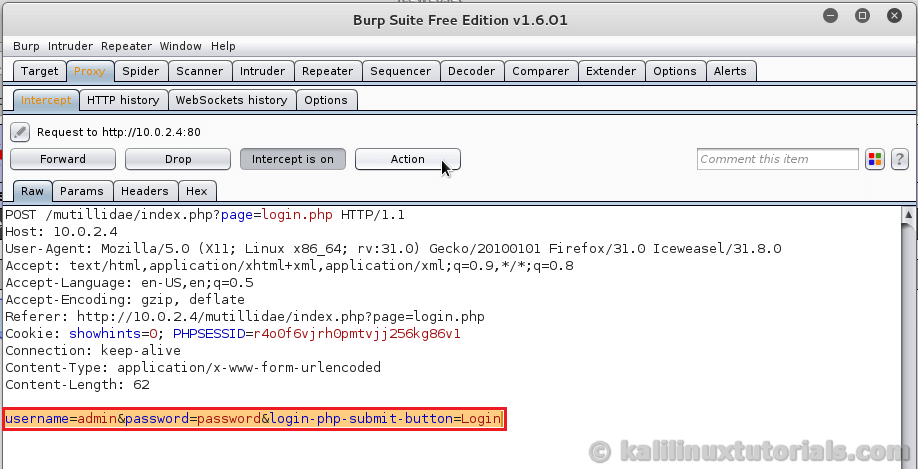
Step 2: Capture the request
After you have configured burp, start intercepting & open the target page.


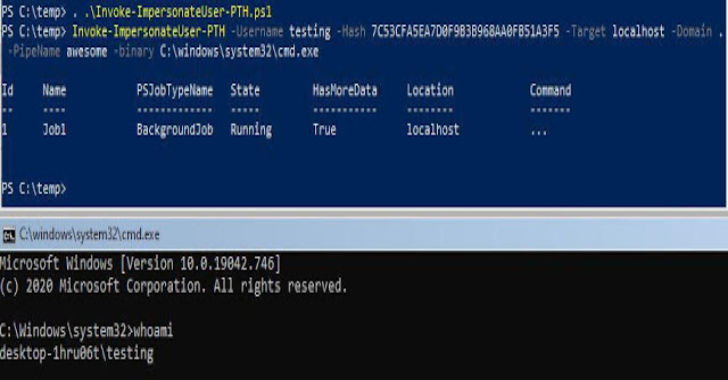
Step 3: Capture the POST request
Capture the POST request where the username & password is supplied to the web-application. This can occasionally be a GET request also. Anyway the idea is we need to capture a request in which some variable value is supplied to the server.
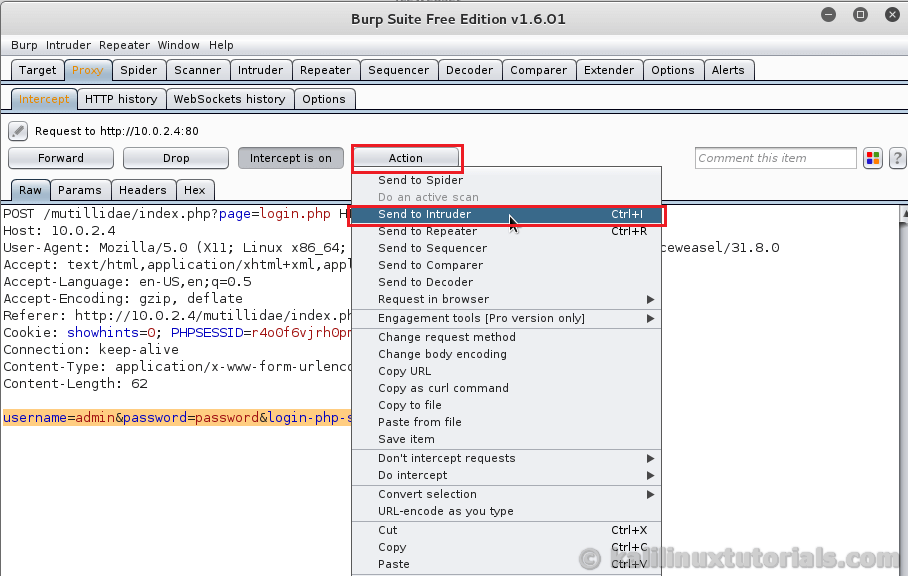
Step 4: Send it to Intruder & Configure Options
Click on the Action button in the top right and select send to intruder.
Then, you will be shown the Intruder options and first target will be shown. This page/tab contains target options like host port use SSL etc. Just cross verify whether the target you are attacking is displayed correctly in this section and proceed to next

Next, go to Positions Tab. This is where we set the variables to be attacked/fuzzed. Burp will automatically populate all positions where a fuzz test can be run. You can customize it by using the options in the Right side of the tab.
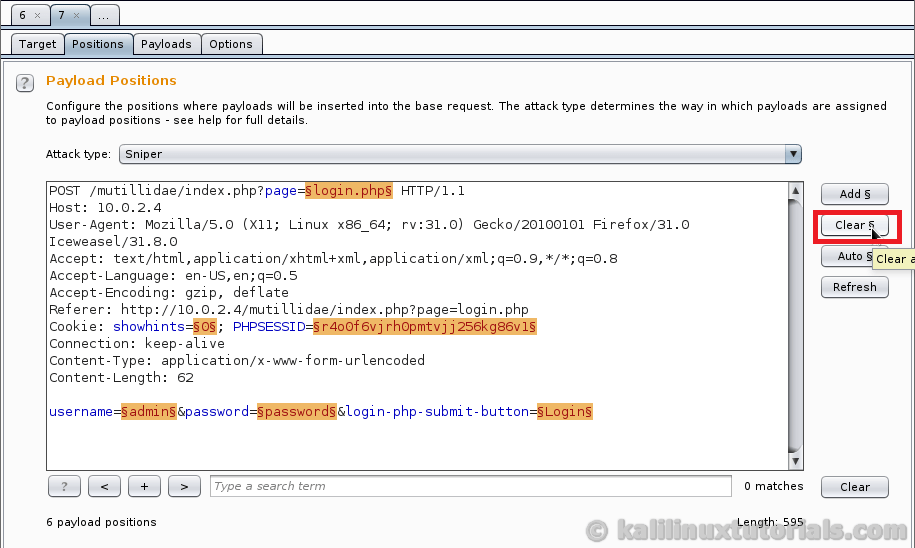
In this case, clear all positions & add position in the password variable. It’s seen at the bottom of the whole request. Do this by clicking the add button. First keep the cursor just after the “=” and click add. Then go to the last letter of that feild and place the cursor there. Add a position there also otherwise the whole content after the position will be taken as a single position. Just like closing brackets in programing or in Maths make sure to open a position and close it.

Once the position is set, confirm whether the Attack type is Sinper. This attack type works just like sniper gun. It fires the payload precisely at a single point. If you have multiple positions, it will fire the payload at the first position and then move on to the second and so on.(One at a time). Speaking of payload, keep reading, it will be explained in the next para so move on to the Payloads tab.
The Payloads tab is where you set the wordlist or list of variables to be run against the payload positions we set previously. There are numerous possibilities & combinations you can try here. You can load a list containing all the words or strings, or you can generate words based on the characters you supply etc. It can be specified in the Payload type drop down menu. Try browsing trhough all of them and you will understand the power of Intruder. For now we supply a simple list. Select the payload type as simple list & click the load button to open an explorer window. Select your wordlist that contains passwords. In Kali, sme default wordlists are supplied inside “/usr/share/wordlists/”. For this one I have selected, “/usr/share/wordlists/metasploit-jtr/password.lst”.

After it has been loaded successfully, you can see the contents of the list in the area beside the Load button. You can also edit the contents using the other buttons present there.
Step 5: Start Attack.
Once everything is set, click the intruder menu from the top and select Start Attack.

Now the intruder attack window pops up which shows the ongoing attack. Here you can see details like HTTP code & length of the response. Now comes the difficult part of analysing the results. Depending upon the target and nature of attack, the results vary. From a bunch of results, you need to analyse it properley. One method to do it is to analyze the pattern of results. For some entries, there may be a difference in the response code or length. This may be a successful attack or may be the failed attack. It depends on the target & nature of attack. In this case, I know the server would return an HTTP 302 if the username & password are right. So I will be on the lookout for this. The idea here is what I said just now, look for patterns & variations from patterns. Check the variation in detail first. It may contain the details of a successful attack.
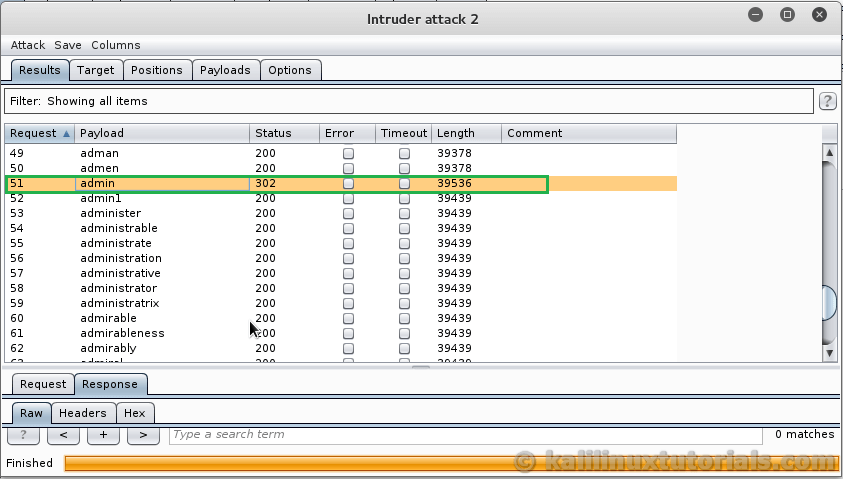
In the above screenshot, we have a 302 response which concludes it may be a successful attack. If you have such a result, click on the particular request from the main area, and look at the results tab below.

Here we have got a cookie with uid=1 for a request with username = admin, which means this particular request has been successful. Look for the payload in the top section or analyze the Request tab to view the password which was supplied. Here in this case, the password is “admin”. So you have successfully carried out a password brute force.
This article has been lengthy and lot of concepts & procedures were involved. Carry out this by yourself along with this post open if you haven’t done this yet. Then you will come across many issues and you will understand the different techniques to run this attack.
If you find this informative or like this, Please share this article.
References & Links