APPLICATIONS
HOT NEWS
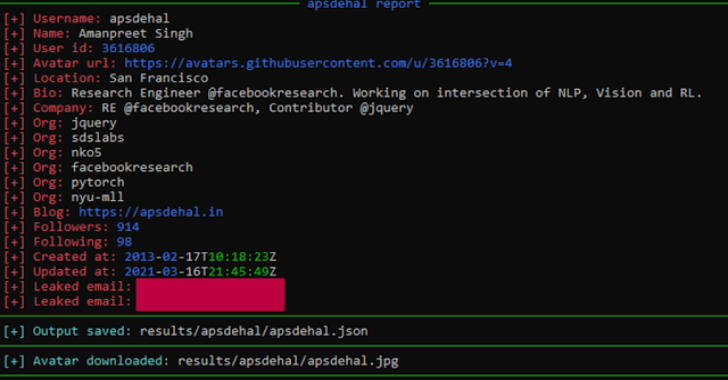
Gitrecon : OSINT Tool To Get Information From A Github Profile
Gitrecon is a OSINT tool to get information from a Github or Gitlab profile and find user's email addresses leaked on commits.
How does this...
© kalilinuxtutorials.com 2025