APPLICATIONS
HOT NEWS
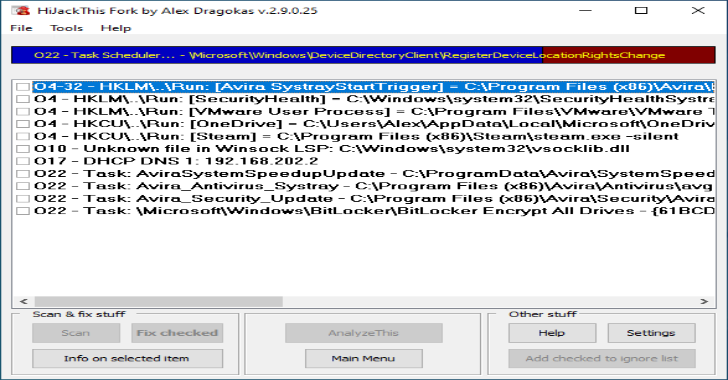
HiJackThis : A Free Utility That Finds Malware, Adware & Other...
HiJackThis Fork is a free utility for Microsoft Windows that scans your computer for settings changed by adware, spyware, malware and other unwanted programs.
HiJackThis...
© kalilinuxtutorials.com 2025





.webp)
.webp)

.webp)
.webp)
.webp)
.webp)
.webp)
.webp)