APPLICATIONS
HOT NEWS
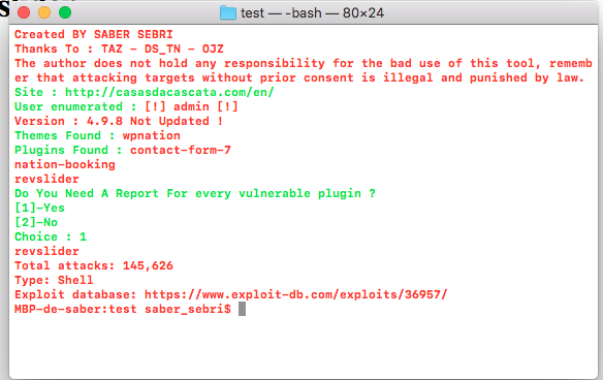
Wpscvn : Wpscvn Is A Tool For Pentesters, Website Owner To...
wpscvn is a tool for pentesters, website owner to test if their websites had some vulnerable plugins or themes
The author does not hold any...
© kalilinuxtutorials.com 2025





.webp)


.webp)

.webp)
.webp)


.webp)