APPLICATIONS
HOT NEWS
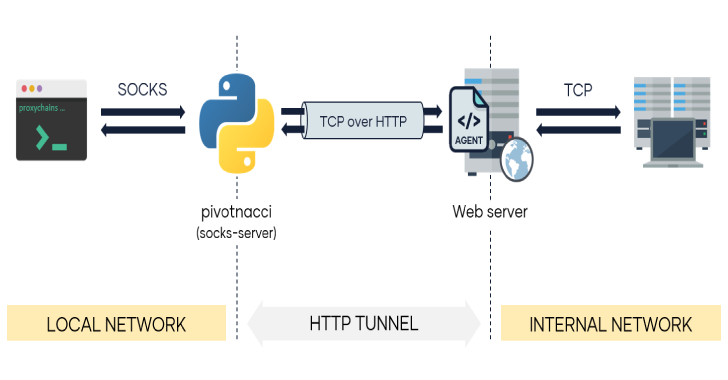
Pivotnacci : A Tool To Make Socks Connections Through HTTP Agents
Pivot into the internal network by deploying HTTP agents. Pivotnacci allows you to create a socks server which communicates with HTTP agents. The architecture...
© kalilinuxtutorials.com 2025