APTRS (Automated Penetration Testing Reporting System) is an automated reporting tool in Python and Django. The tool allows Penetration testers to create a report directly without using the Traditional Docx file. It also provides an approach to keeping track of the projects and vulnerabilities.
Read Documentation here.
Prerequisites
- Python 3.8 and above (https://www.python.org/downloads/release/python-3810/)
- wkhtmltopdf 0.12.6 and above (https://wkhtmltopdf.org/downloads.html)
Installation
The tool has been tested using Python 3.8.10 on Kali Linux 2022.2/3, Ubuntu 20.04.5 LTS, Windows 10/11.
Windows Installation
git clone https://github.com/Anof-cyber/APTRS.git
cd APTRS
install.bat
Linux Installation
git clone https://github.com/Anof-cyber/APTRS.git
cd APTRS
install.sh
Running
Windows
run.bat
Linux
run.sh
Features
- Demo Report
- Managing Vulnerabilities
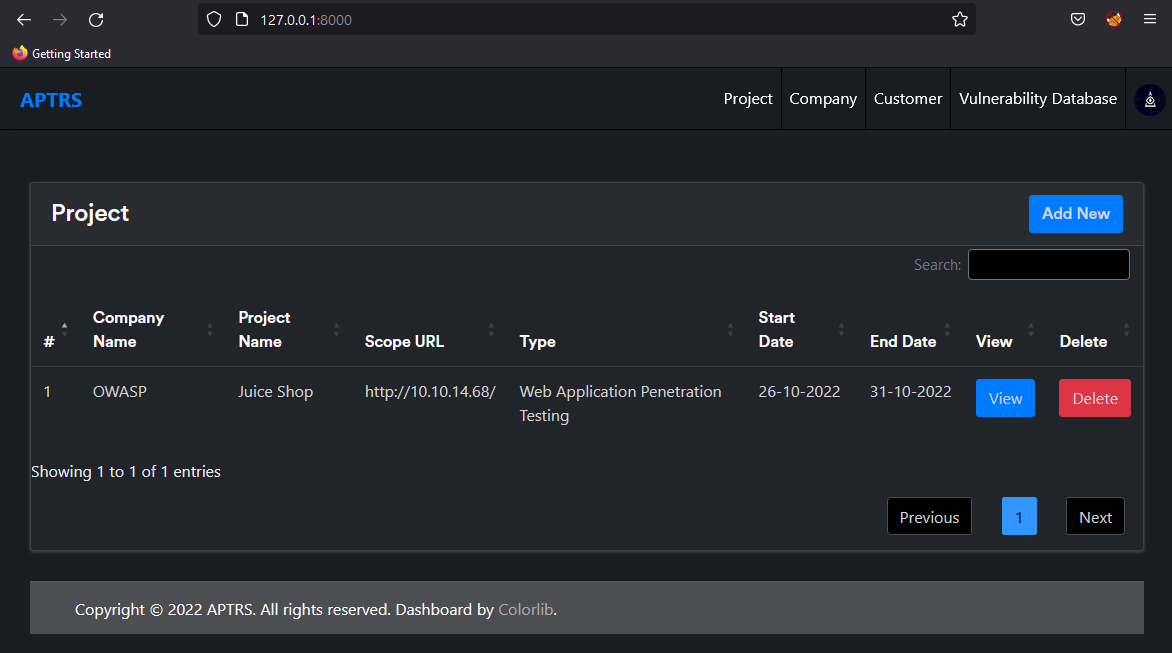
- Manage All Projects in one place
- Create a Vulnerability Database and avoid writing the same description and recommendations again
- Easily Create PDF Reprot
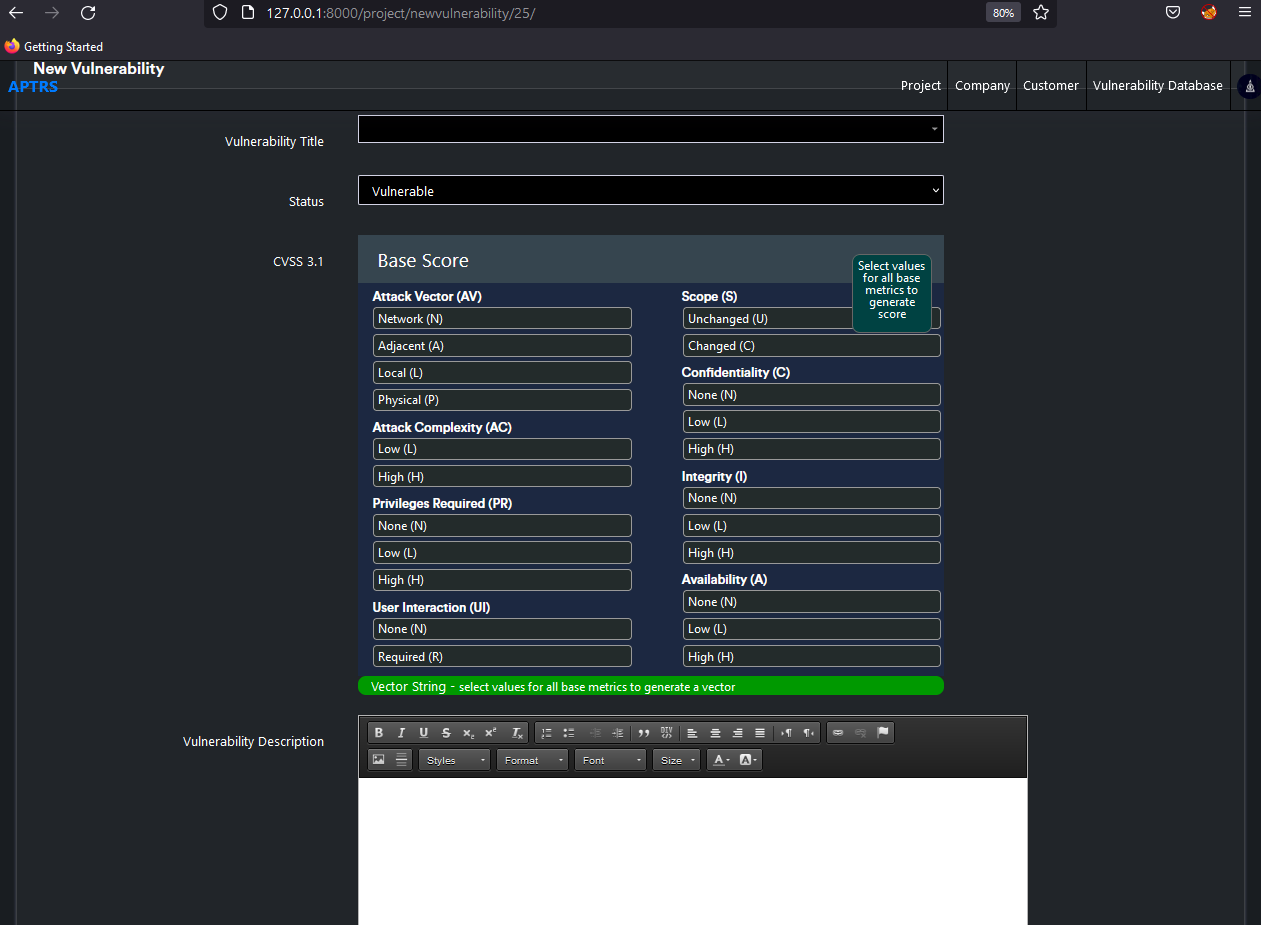
- Dynamically add POC, Description and Recommendations
- Manage Customers and Comapany
Screenshots
Project
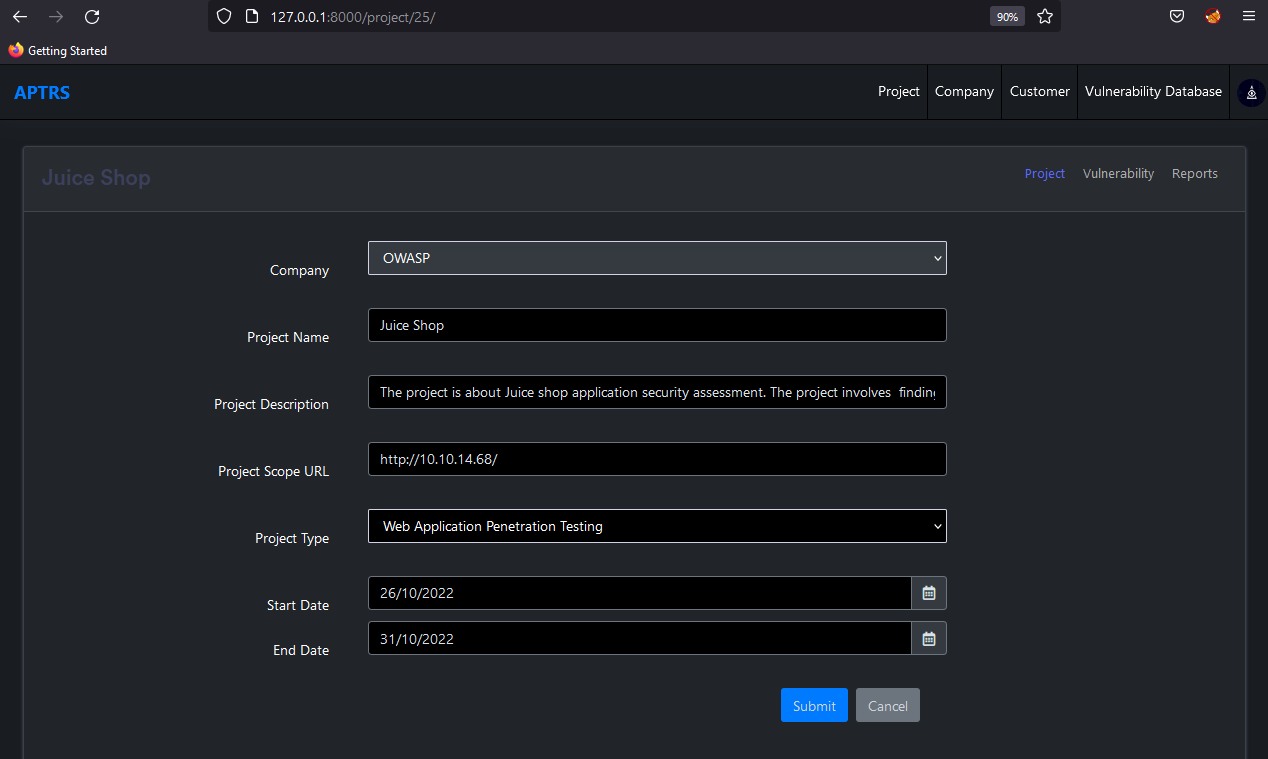
View Project
Project Vulnerability

Project Report
Project Add Vulnerability
Roadmap
- Improving Report Quality
- Bulk Instance Upload
- Pentest Mapper Burp Suite Extension Integration
- Allowing Multiple Project Scope
- Improving Code, Error handling and Security
- Docker Support
- Implementing Rest API
- Project and Project Retest Handler
- Access Control and Authorization
- Support Nessus Parsing
Authors
- Sourav Kalal