APPLICATIONS
HOT NEWS
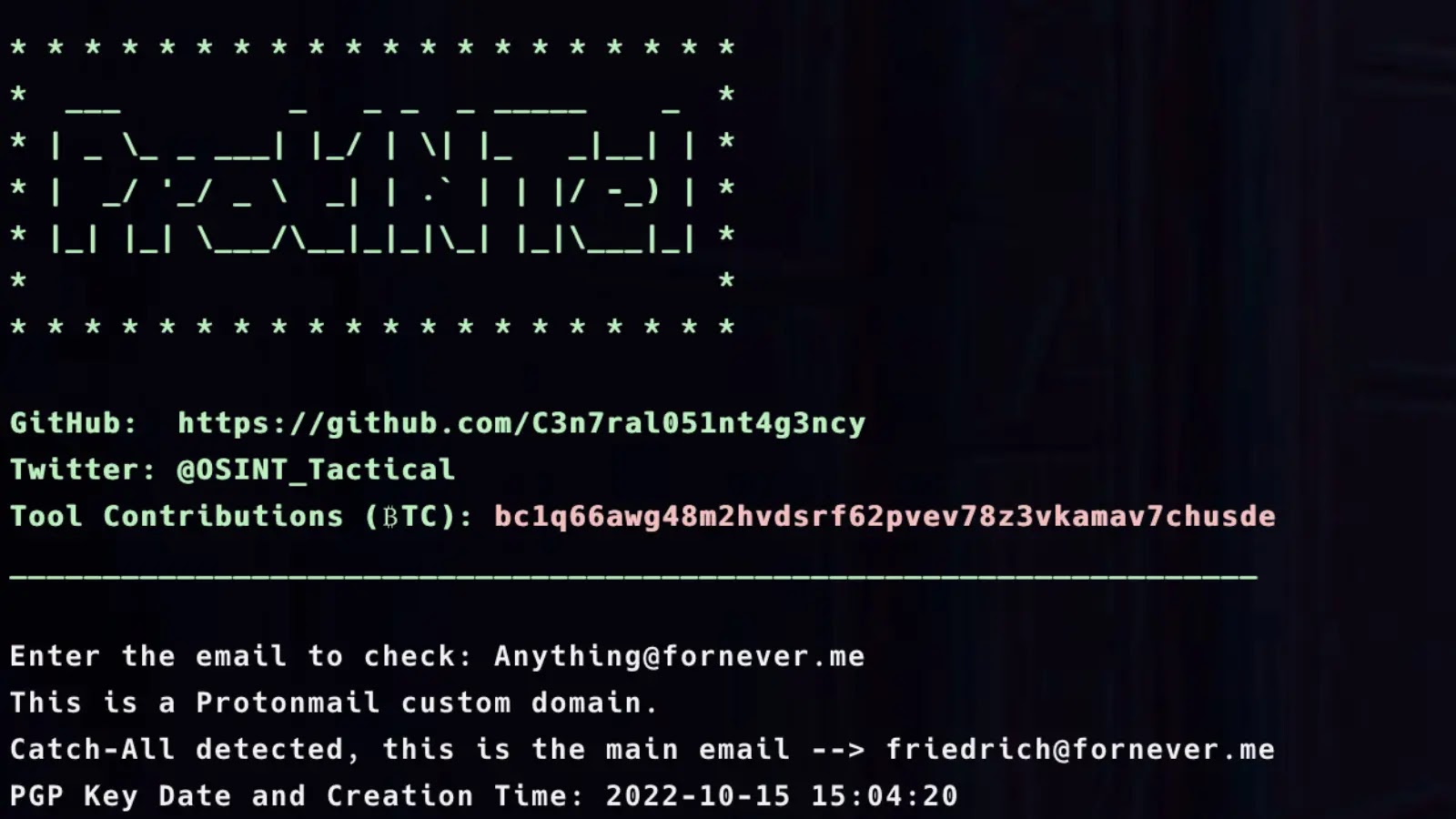
Wsh : Web Shell Generator And Command Line Interface
wsh (pronounced woosh) is a web shell generator and command line interface. This started off as just an http client since interacting with webshells...
© kalilinuxtutorials.com 2025










.webp)
.webp)
