APPLICATIONS
HOT NEWS
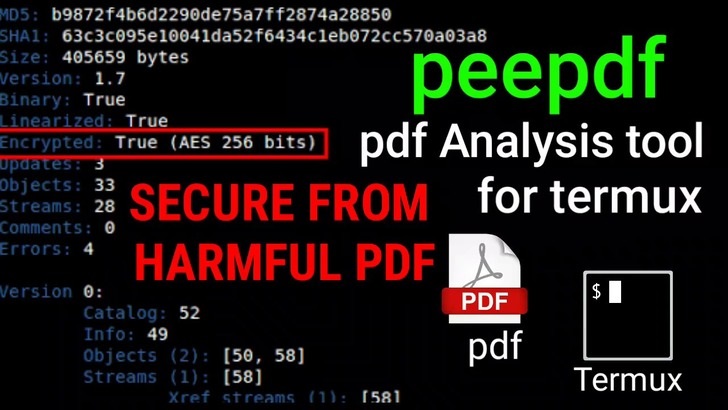
PEEPDF : A One Stop Tool for PDF Document Forensic Analysis
Ravi Sankar - 0
Peepdf is a tool for the forensic analysis of pdf documents. Most social engineering attacks use a malicious PDF document embedded with java scripts...
© kalilinuxtutorials.com 2025









.webp)
.webp)

.webp)
.webp)