APPLICATIONS
HOT NEWS
DumpMDEConfig – Extracting Microsoft Defender Configuration And Logs With PowerShell Script
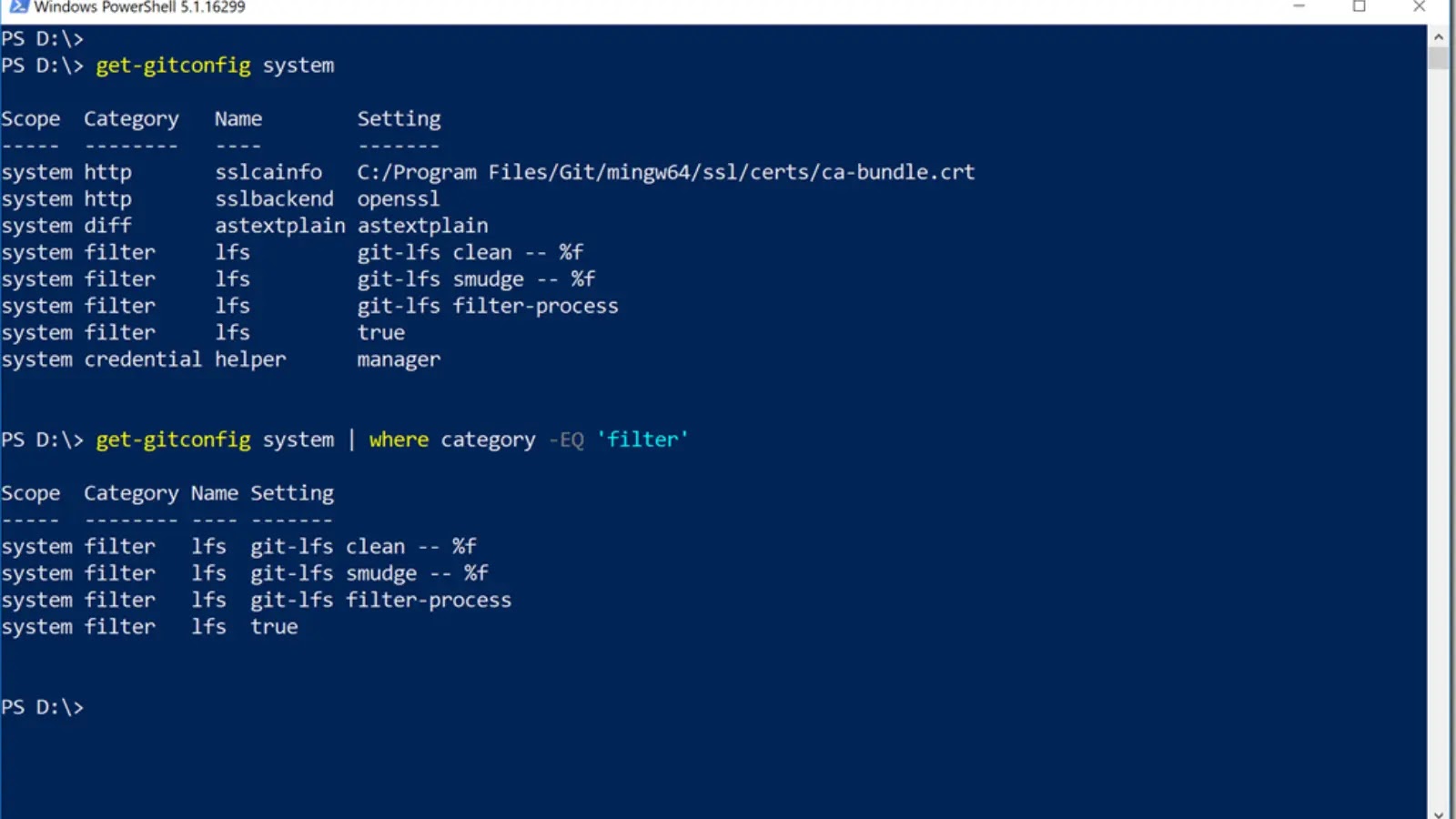
Invoke-DumpMDEConfig is a PowerShell script designed to extract and display Microsoft Defender configuration and logs, including excluded paths, enabled ASR rules, allowed threats, protection history,...
© kalilinuxtutorials.com 2025





.webp)
.webp)

.webp)
.webp)
.webp)



.webp)