Web Application firewalls are typically firewalls working on the application layer which monitors & modifies HTTP requests. The key difference is that WAFs work on Layer 7 – Application Layer of the OSI Model.
Basically, all WAFs protect against different HTTP attacks & queries like SQLi & XSS. Since the firewall is able to detect HTTP methods, SQL queries & other scripts put as input to different forms in a website, it can filter out the requests just like a normal firewall would do. One can implement a policy on what should be permitted & what not as input through a website.
A WAF will be typically present in a web application where there is Strict Transport Security enabled like a banking website or an e-commerce website. While conducting a pentest, detecting the waf comes under recon, and mapping the web application architecture. One should detect the presence of a WAF & evaluate it in case of a Black Box testing. This plays a crucial part in determining the methods to proceed during a Web-Application Penetration Test.
Wafw00f is simply a python tool which automates a set of procedures used in finding a WAF. Wafw00f simply queries a web server with a set of HTTP requests & methods. It analyses the responses from them & detects the firewall in place.
Homepage: https://github.com/sandrogauci/wafw00f
Options:
Syntax : wafw00f url1 [url2 [url3 ... ]] example: wafw00f http://www.victim.org/
-h, --help show this help message and exit -v, --verbose enable verbosity - multiple -v options increase verbosity -a, --findall Find all WAFs, do not stop testing on the first one -r, --disableredirect Do not follow redirections given by 3xx responses -t TEST, --test=TEST Test for one specific WAF -l, --list List all WAFs that we are able to detect --xmlrpc Switch on the XML-RPC interface instead of CUI --xmlrpcport=XMLRPCPORT Specify an alternative port to listen on, default 8001 -V, --version Print out the version
Lab: Detect WAFs in some eCommerce websites.
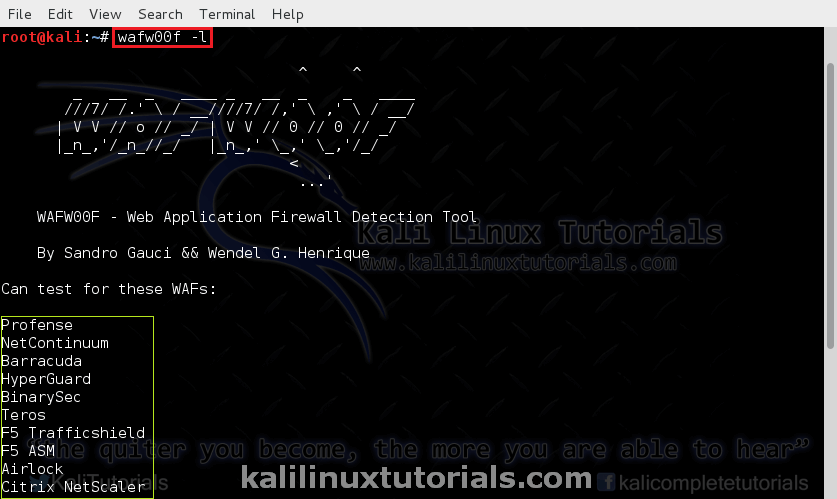
First, we’ll see the list of firewalls readily supported. Even though a specific firewall is not supported by wafw00f, it detects the presence of one.
Command: wafw00f -l
Let’ s begin
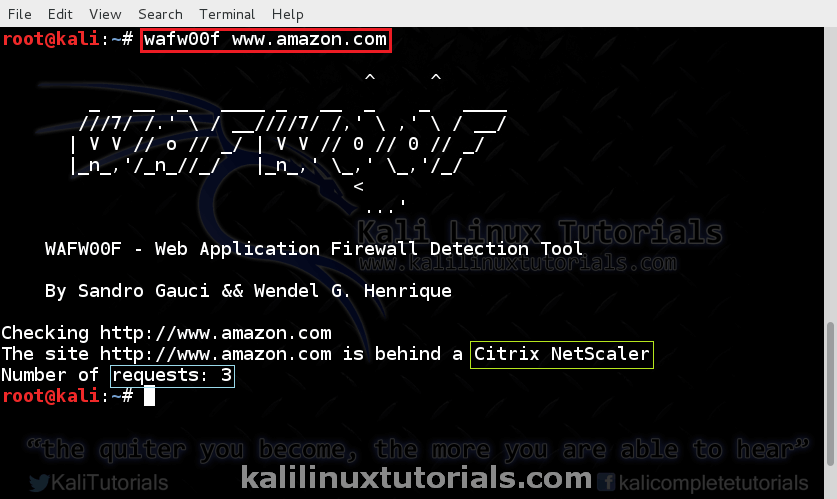
Command: wafw00f www.amazon.com
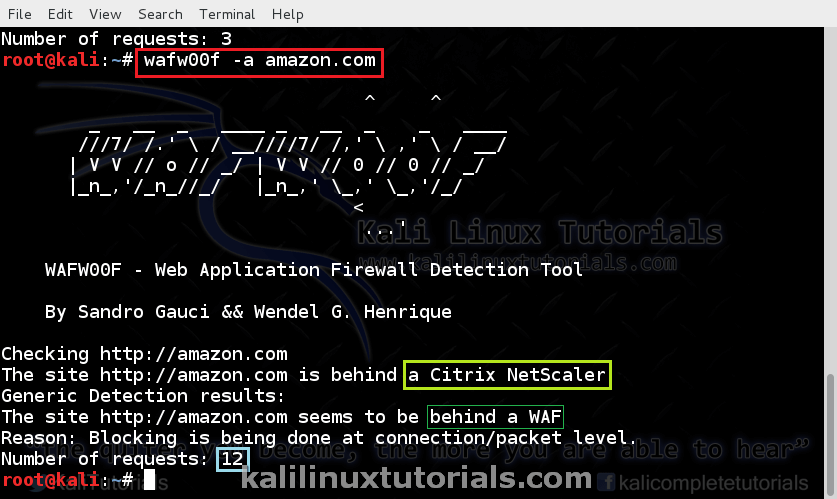
Aggressively Test for firewalls. This is useful in identifying multiple firewalls.
Command: wafw00f -a www.amazon.com
Note the number of requests in this & previous cases.
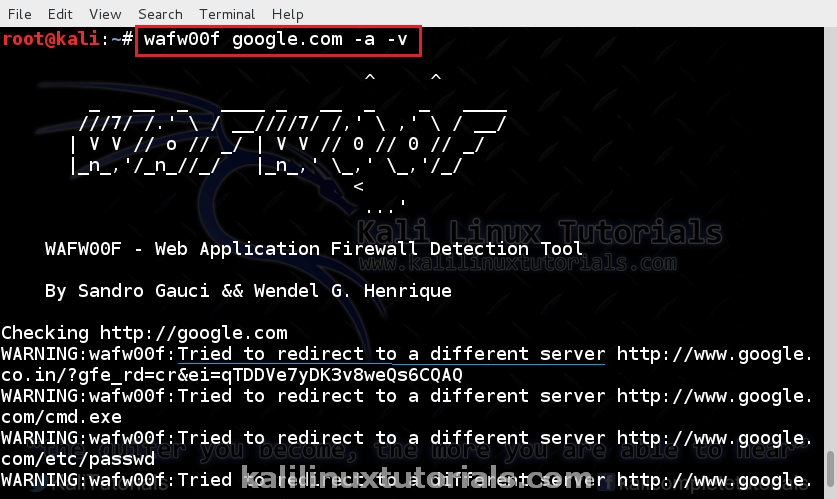
Let’s try it on Google
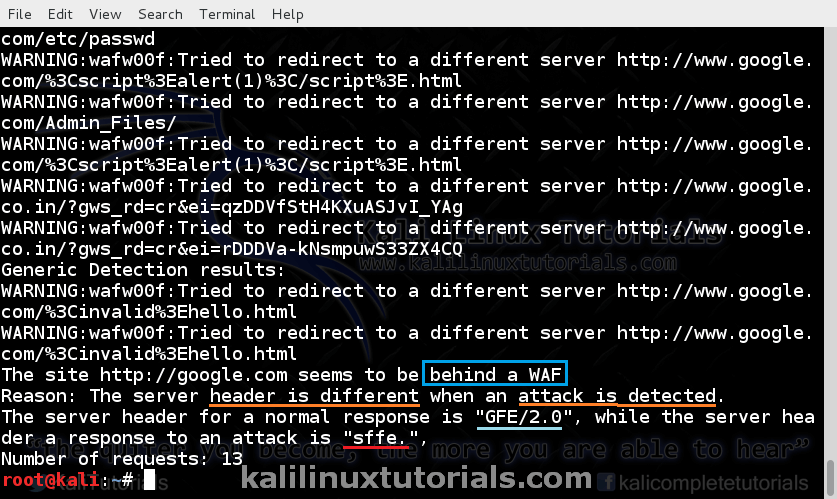
Command: wafw00f google.com -a -v
Giving the verbose option, lets you see the queries. Increase no of v (-vv) to increase verbosity.
Here a firewall is detected from the response headers. Increase the no of v to see the actual headers.
This procedure is important during a pentest as said earlier. Fingerprinting the waf also helps to identify any known vulnerabilities in Web Application Firewalls if any exists.























.webp)
.webp)
