DeimosC2 is a post-exploitation Command & Control (C2) tool that leverages multiple communication methods in order to control machines that have been compromised.
DeimosC2 server and agents works on, and has been tested on, Windows, Darwin, and Linux. It is entirely written in Golang with a front end written in Vue.js.
Listener Features
- Each listener has it’s own RSA Pub and Private key that is leveraged to wrap encrypted agent communications.
- Dynamically generate agents on the fly
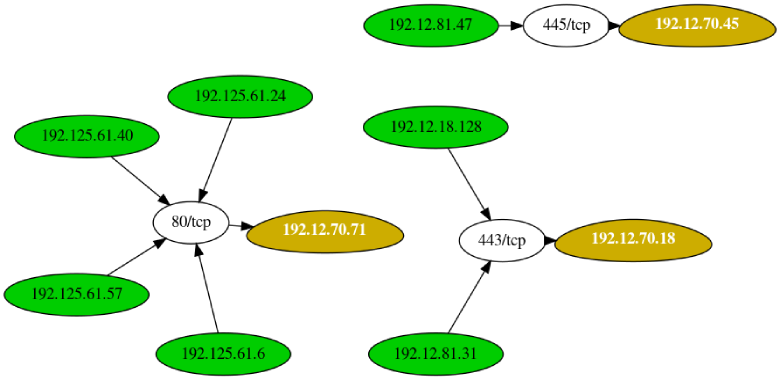
- Graphical map of listener and agents that are tied to it
Agent Features
- Agent list page to give high level overview
- Agent interaction page containing info of agent, ability to run jobs against agent, filebrowser, loot data, and ability to add comments
Supported Agents
- TCP
- HTTPS
- DoH (DNS over HTTPS)
- QUIC
- Pivot over TCP
Frontend Features
- Multi-User support with roles of admin and user
- Graphs and visual interaction with listeners and agents
- Password length requirements
- 2FA Authentication using Google MFA
- Websocket API Calls
Getting Started and Help
You can download the latest release and view the wiki for any assistance getting started or running the C2.
Submitting Issues
We welcome issues to be opened to help improve this project and keep it going. For bugs please use the template.
Authors
- Chase Dardaman (@CharlesDardaman)
- Quentin Rhoads-Herrera (@paragonsec)
- Elvira Sheina (developeruz)
- Blase Brignac (@BlaiseBrignac)
Credits
In order to develop this we used some of the awesome work of others. Below is a list of those we either used their code or were inspired by. If we missed you please let us know so we can add your name!
- lsassy by @HackAndDo used for some Windows modules
- goDoH by @leonjza from SensePost used for DoH
- BishopFox Sliver used in some places as they already did a fanstastic job
- Merlin used for reflective DLLs support
- dgoogauth used for the 2FA functionality
- gobfuscate used to support agent obfuscation
- Stack Overflow because isn’t this how we develop now?
Disclaimer
This program should only be used on environments that you own or have explicit permission to do so. Neither the authors, nor Critical Start, Inc., will be held liable for any illegal use of this program.










.png)