APPLICATIONS
HOT NEWS
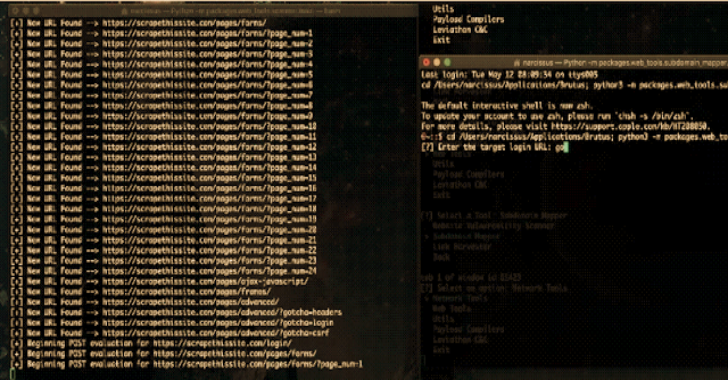
Shells : Little Script For Generating Revshells
Shells is a script for generating common revshells fast and easy. Especially nice when in need of PowerShell and Python revshells, which can be...
© kalilinuxtutorials.com 2025













.png)