APPLICATIONS
HOT NEWS
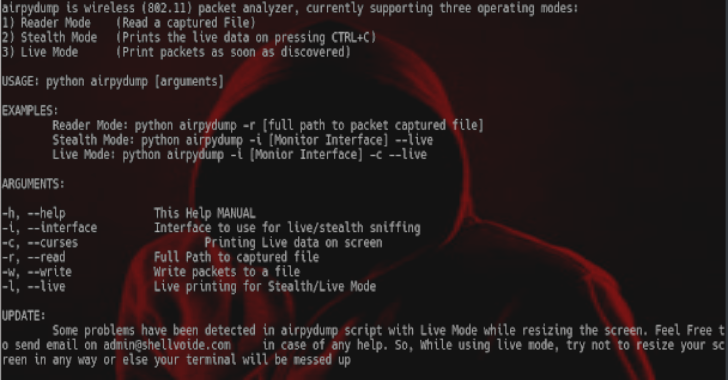
AirpyDump : Analyse Wireless Packets On The Fly
AirpyDump is a wireless packet analyzer, providing the interface most likely that of airodump-ng from aircrack suite. It currently provides three working modes which...
© kalilinuxtutorials.com 2025





.webp)
.webp)



.webp)
.webp)
.webp)
.webp)
.webp)