SSH Auditor is the best way to scan for weak ssh passwords on your network. SSH Auditor will automatically:
- Re-check all known hosts as new credentials are added. It will only check the new credentials.
- Queue a full credential scan on any new host discovered.
- Queue a full credential scan on any known host whose ssh version or key fingerprint changes.
- Attempt command execution as well as attempt to tunnel a TCP connection.
- Re-check each credential using a per credential
scan_interval– default 14 days.
It’s designed so that you can run ssh-auditor discover + ssh-auditor scanfrom cron every hour to to perform a constant audit.
Also ReadManticore : Symbolic Execution Tool
Installation SSH Auditor
$ brew install go # or however you want to install the go compiler
$ go get github.com/ncsa/ssh-auditoror Build from a git clone
$ go build
Build A Static Binary Including SQLite
$ make static
Ensure you can use enough file descriptors
$ ulimit -n 4096
Create initial database and discover ssh servers
$ ./ssh-auditor discover -p 22 -p 2222 192.168.1.0/24 10.0.0.1/24
Add credential pairs to check
$ ./ssh-auditor addcredential root root
$ ./ssh-auditor addcredential admin admin
$ ./ssh-auditor addcredential guest guest --scan-interval 1 #check this once per dayTry credentials against discovered hosts in a batch of 20000
$ ./ssh-auditor scan
Output a report on what credentials worked
$ ./ssh-auditor vuln
RE-Check credentials that worked
$ ./ssh-auditor rescan
Output a report on duplicate key usage
$ ./ssh-auditor dupesVideo Demos
Earlier demo showing all of the features
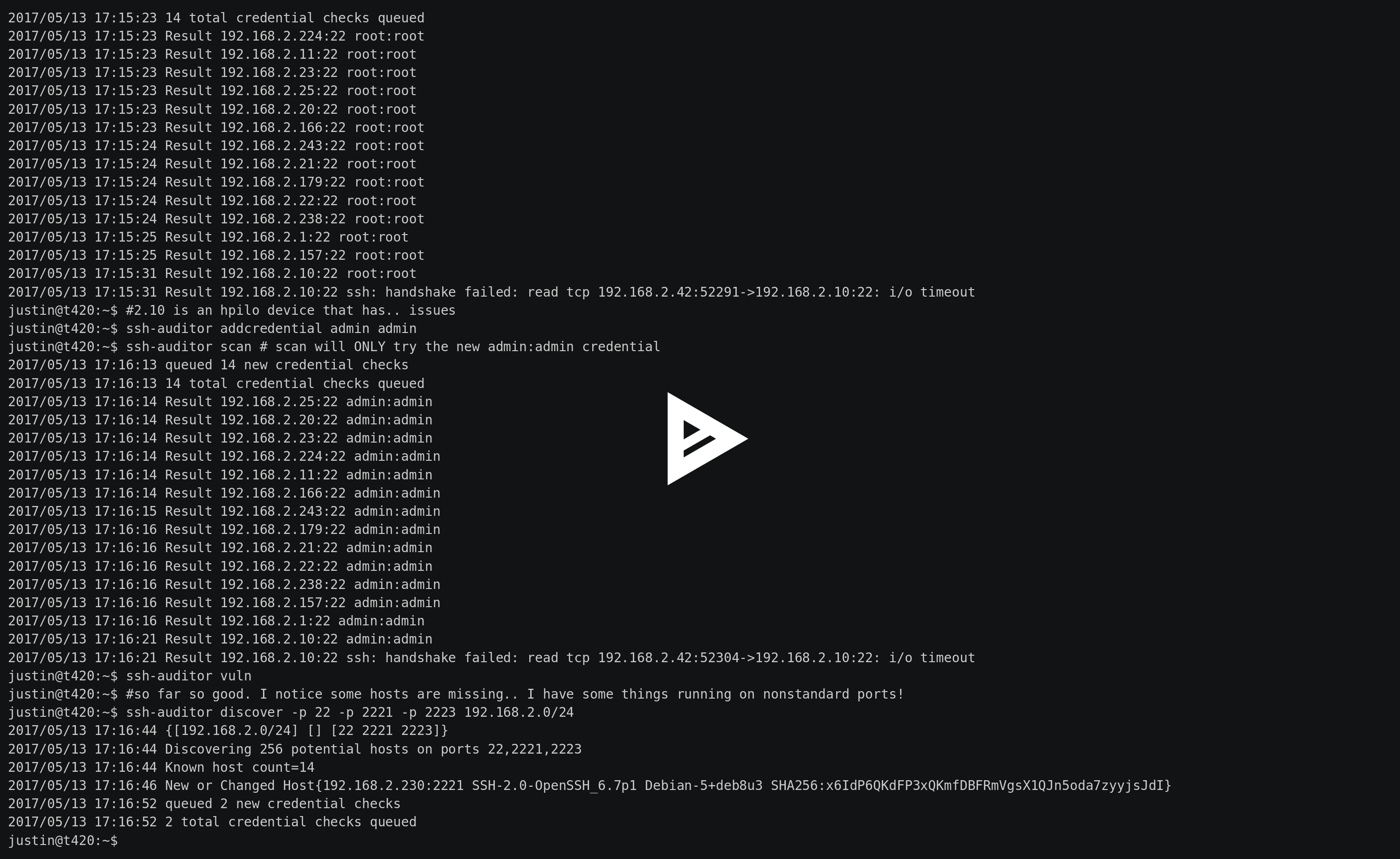 Demo showing improved log output
Demo showing improved log output
![]() You can follow us on Linkedin, Twitter, Facebook for daily Cybersecurity updates also you can take the Best Cybersecurity courses online to keep your self-updated.
You can follow us on Linkedin, Twitter, Facebook for daily Cybersecurity updates also you can take the Best Cybersecurity courses online to keep your self-updated.