APPLICATIONS
HOT NEWS
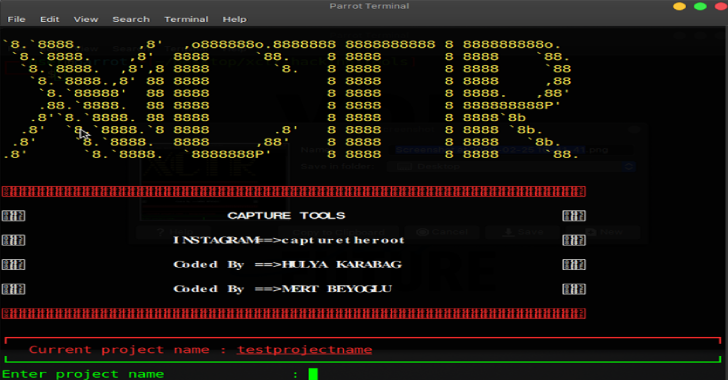
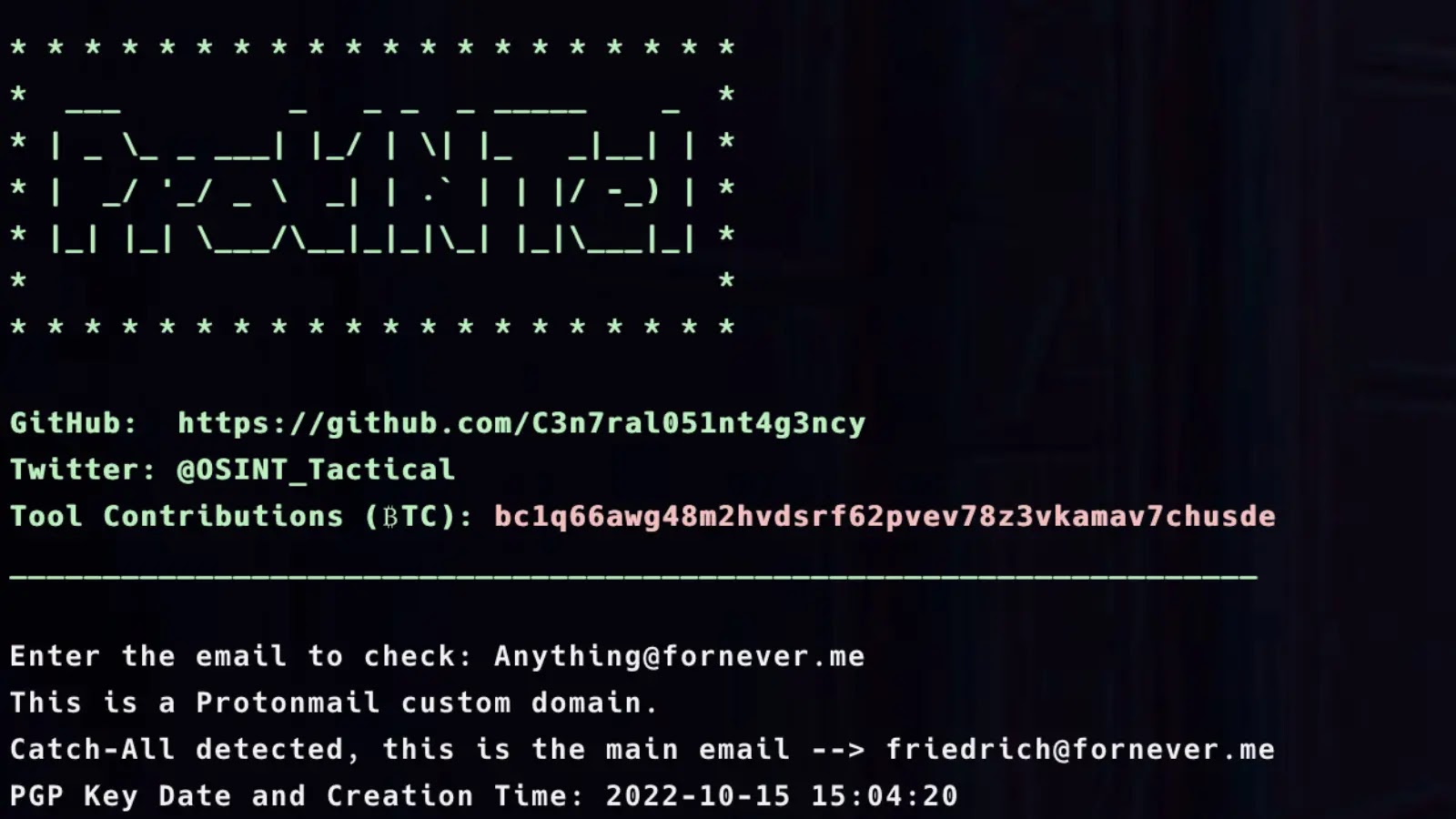
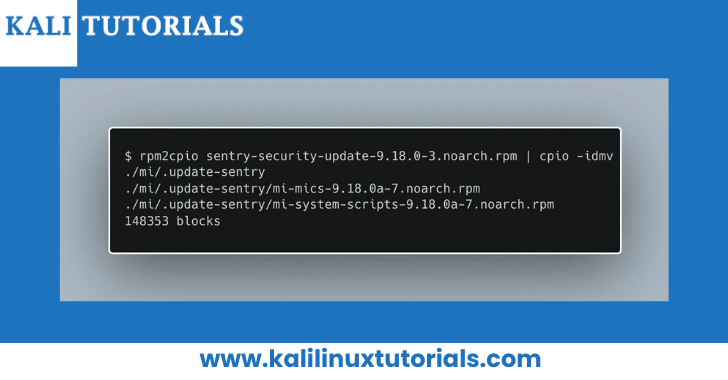
XCTR Hacking Tools 2020
XCTR Hacking Tools initially, you need to create a project where you will save everything. All of the collected information is saved as...
© kalilinuxtutorials.com 2025







.webp)
.webp)



.webp)