APPLICATIONS
HOT NEWS
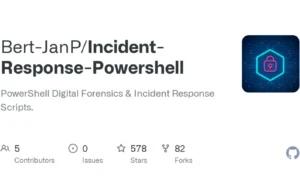
Powershell Digital Forensics And Incident Response
PowerShell has emerged as a vital tool in Digital Forensics and Incident Response (DFIR), offering robust capabilities for automating data collection, analysis, and containment...
© kalilinuxtutorials.com 2025