APPLICATIONS
HOT NEWS
Invoke-DNSteal : Simple And Customizable DNS Data Exfiltrator
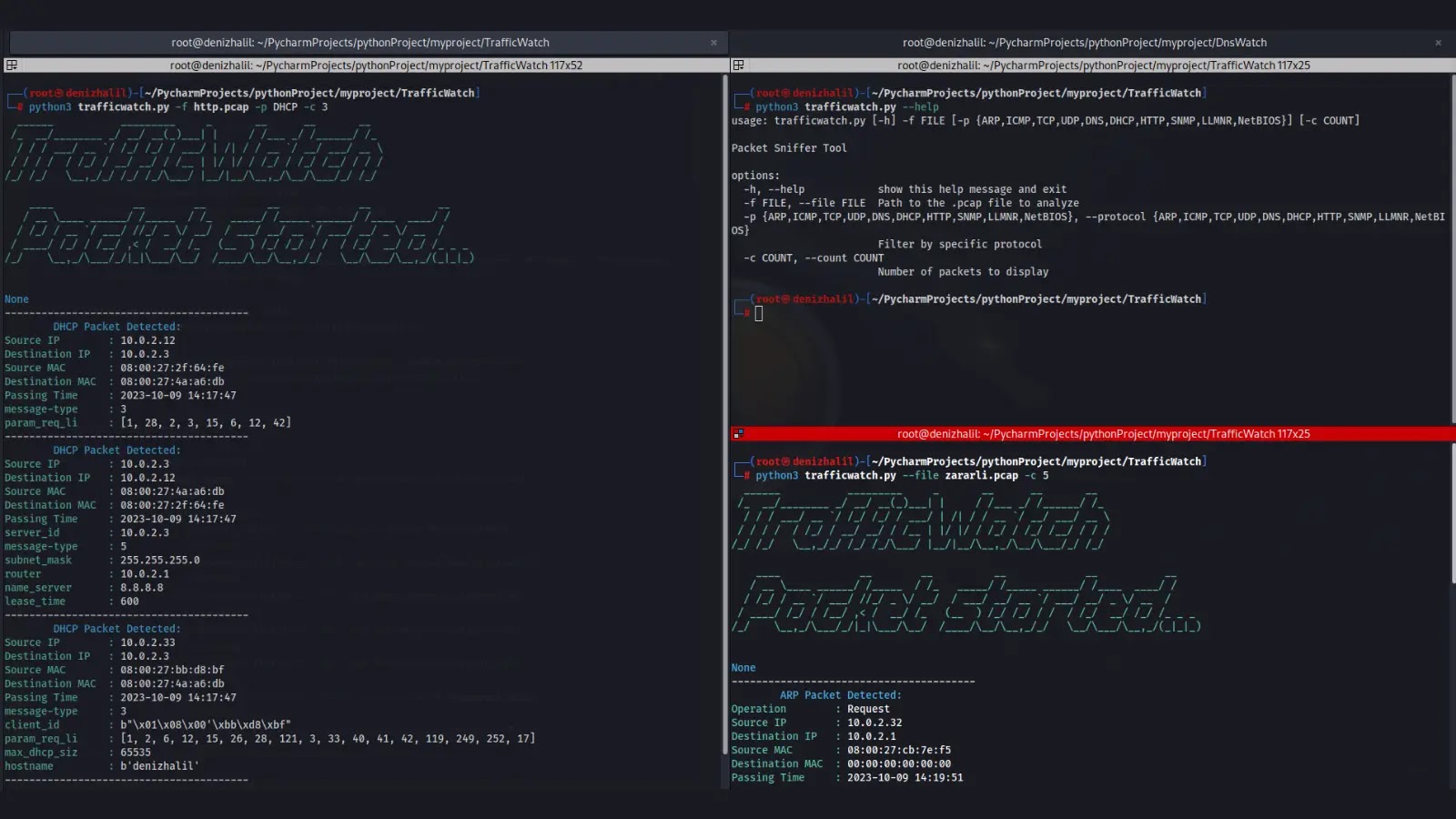
Invoke-DNSteal is a Simple & Customizable DNS Data Exfiltrator.
This tool helps you to exfiltrate data through DNS protocol over UDP and TCP, and lets you...
© kalilinuxtutorials.com 2025










.webp)
