APPLICATIONS
HOT NEWS
Security RAT : Tool For Handling Security Requirements In Development
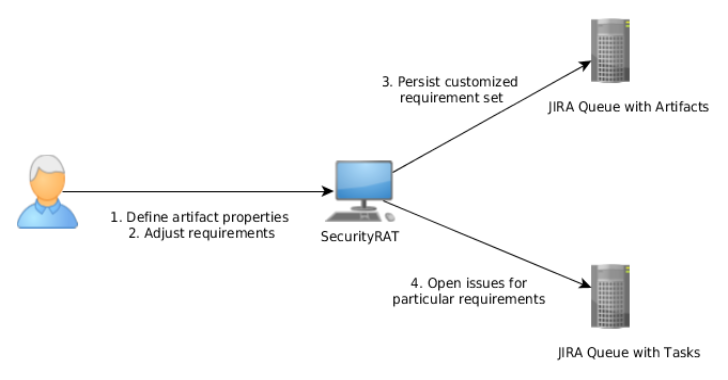
OWASP Security RAT (Requirement Automation Tool) is a tool supposed to assist with the problem of addressing security requirements during application development. The typical use...
© kalilinuxtutorials.com 2025






.webp)


.png)
.png)

.png)